Best rootkit removal tool is essential for anyone seeking to safeguard their system from the hidden threats posed by malicious software. Rootkits, notorious for their stealthy infiltration and deep control over infected systems, can severely compromise security and privacy. Understanding the nature of rootkits, their various types, and common behaviors is the first step in defending against these insidious threats.
By exploring the critical importance of rootkit removal, we can uncover the risks associated with neglecting these hidden dangers. Users will learn how rootkits can jeopardize both personal and organizational data security, alongside identifying the alarming symptoms that signal a potential infection. As we delve into the features of effective removal tools and the top selections available, readers will gain valuable insights into safeguarding their systems.
Introduction to Rootkits: Best Rootkit Removal Tool
Rootkits are a type of malicious software designed to gain unauthorized access to a computer system while concealing their presence. They are a significant threat to system security, as they can allow attackers to control the infected systems without the user’s knowledge. Rootkits can be particularly insidious because they operate at a low level in the system, often modifying the operating system itself to hide their presence.
There are several types of rootkits, including user-mode rootkits, kernel-mode rootkits, and firmware rootkits. User-mode rootkits operate within the user space and can modify applications and processes, while kernel-mode rootkits operate at the core of the operating system, allowing for deeper control. Firmware rootkits are embedded in the hardware, making them particularly difficult to detect and remove.
Common behaviors associated with rootkits include altering system files, installing additional malware, and intercepting network traffic. Their effects can range from performance degradation and unauthorized data access to total system compromise, highlighting the importance of rootkit detection and removal.
Importance of Rootkit Removal

The potential risks of rootkits are significant if left untreated. They can lead to data breaches, loss of sensitive information, and unauthorized access to personal and organizational resources. Rootkits can remain undetected for extended periods, making the damage they cause even more severe.
Rootkits have a profound impact on both personal and organizational data security. They can facilitate the theft of personal data, financial information, and intellectual property, leaving individuals and organizations vulnerable to identity theft and financial loss. Furthermore, organizations may face legal repercussions if they fail to protect customer data.
Indicators of a rootkit infection can include unexplained system slowdowns, unfamiliar applications running in the background, and suspicious network activity. Recognizing these signs early is crucial for preventing further damage and ensuring a swift response.
Features of the Best Rootkit Removal Tools
Effective rootkit removal tools share several key features that enhance their efficacy. These features include:
- Deep Scanning Capabilities: The ability to scan the entire system, including hidden files and processes, is essential for detecting rootkits.
- Real-Time Protection: Continuous monitoring of system activities helps to prevent rootkit installations.
- User-Friendly Interface: An intuitive design allows users of all skill levels to navigate the tool effortlessly.
- Automatic Updates: Regular updates ensure the tool can detect the latest threats and vulnerabilities.
When comparing different tools, detection capabilities and user-friendliness are pivotal. A tool may excel in detection but could be difficult for average users to utilize, diminishing its overall effectiveness. Furthermore, the importance of regular updates cannot be overstated, as new rootkit variants are constantly being developed.
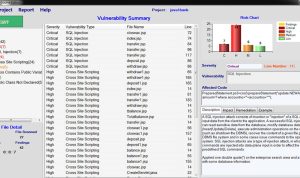
Top Rootkit Removal Tools on the Market
A detailed comparison of the leading rootkit removal tools reveals their distinct features, pricing, and compatibility:
| Tool Name | Features | Pricing | Compatibility |
|---|---|---|---|
| Malwarebytes | Real-time protection, deep scans, automatic updates | $39.99/year | Windows, macOS, Android |
| Kaspersky | Cloud-based scanning, heuristic analysis, user-friendly interface | $59.95/year | Windows, macOS, Android |
| Bitdefender | Multi-layer ransomware protection, advanced threat defense | $49.99/year | Windows, macOS, Android |
User reviews and experiences highlight the effectiveness of these tools in removing rootkits. Malwarebytes is often praised for its user-friendly approach, while Kaspersky is recognized for its comprehensive security suite. Bitdefender receives accolades for its advanced features, making it a strong contender for users needing robust protection.
Step-by-Step Guide to Using Rootkit Removal Tools
Using a popular rootkit removal tool involves several key steps to ensure effective operation:
1. Download and Install the Tool: Visit the official website and download the latest version of the rootkit removal tool.
2. Backup Data: Before running the tool, it’s crucial to back up important files to prevent data loss.
3. Launch the Tool: Open the application and initiate a full system scan.
4. Review Scan Results: Once the scan is complete, review the detected threats and select the appropriate actions for removal.
5. Follow Instructions: Follow the on-screen instructions to complete the removal process.
Precautions before running a rootkit removal tool include ensuring that other security software is temporarily disabled to avoid conflicts. Common issues during removal might involve file access errors, which can usually be resolved by running the tool in safe mode.
Prevention Strategies Against Rootkits
Preventing rootkit infections requires a proactive approach. Best practices include:
- Regularly updating software and operating systems to patch vulnerabilities.
- Utilizing reliable antivirus solutions alongside rootkit removal tools for layered security.
- Educating users about the dangers of phishing attacks and suspicious downloads.
- Implementing firewalls and network security protocols to monitor incoming and outgoing traffic.
Regular system updates and security patches play a vital role in rootkit prevention, as many rootkits exploit known vulnerabilities. Additionally, reliable antivirus solutions can provide an essential defense against a wide range of malware threats, including rootkits.
Real-World Case Studies
Analyzing real-world cases of rootkit infections provides valuable insights into their impacts and the effectiveness of removal efforts. For example, a notable case involved a corporation whose network was compromised by a rootkit that siphoned off sensitive customer data. After employing a rootkit removal tool, they managed to eliminate the threat but suffered significant reputational damage.
Lessons learned from these cases emphasize the importance of swift detection and removal. Organizations should develop a comprehensive response strategy to prepare for potential rootkit threats, including regular security audits and employee training on cybersecurity best practices.